About the D3FEND Knowledge Graph Project
In project work for our sponsors, we have repeatedly encountered the need for a model that can precisely specify cybersecurity countermeasure components and capabilities. Furthermore, it is necessary that practitioners know not only what threats a capability claims to address, but specifically how those threats are addressed from an engineering perspective, and under what circumstances the solution would work. This knowledge is essential to estimate operational applicability, identify strengths and weaknesses, and develop enterprise solutions comprising multiple capabilities.
To address this recurring need in the near-term, we created D3FEND, a framework in which we encode a countermeasure knowledge base, but more specifically, a knowledge graph. The graph contains semantically rigorous types and relations that define both the key concepts in the cybersecurity countermeasure domain and the relations necessary to link those concepts to each other. We ground each of the concepts and relations to particular references in the cybersecurity literature.
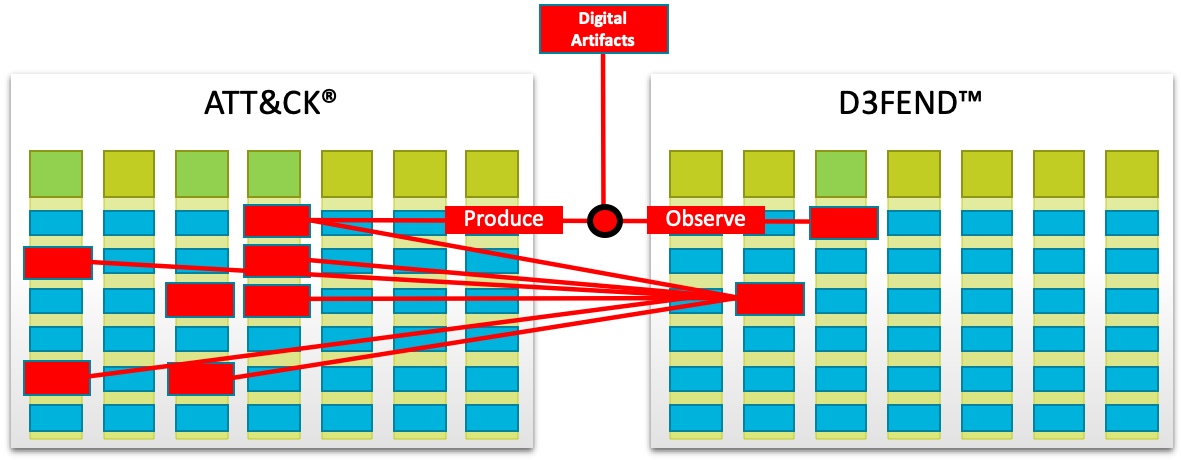
Numerous sources of research and development literature, to include a targeted sample of over 500 countermeasure patents from the U.S. Patent Office from the years 2001 to 2018, served as the source material to build this knowledge graph. To demonstrate the value of this approach in practice, the graph supports queries that can inferentially map cybersecurity countermeasures to offensive tactics, techniques, and procedures. Our longer-term vision is to leverage the linked open data available on research literature and apply machine learning, in particular semi-supervised methods, to assist in maintaining the D3FEND knowledge graph over time. Finally, we welcome community feedback on D3FEND.
Research Funding
This research was funded by the Cybersecurity Directorate of the National Security Agency under contract W56KGU-18-D-0004.